A woman strolls into a grocery store, thinking about grabbing some apples. Before she even reaches the produce aisle, a security camera has scanned her face. Whether the system is checking for shoplifters or simply logging her arrival, her face has joined a digital ledger, a trace she can’t easily erase. Retailers, banks, airports, stadiums and office buildings are doing the same.
But what if the woman’s facial information is stolen or misused? If a cybercriminal steals her password, she can change it. If they acquire her credit card number, she can cancel the card. But she can’t reset or revoke the appearance of her cheekbones.
Facial recognition systems don’t keep actual images. They convert a face into a mathematical template that maps the positions and proportions of the face’s features. When another camera scans a person later, the system checks their live face against these templates to confirm an identity.
In my work as a cybersecurity professor at Rochester Institute of Technology, I have found that even though templates are more secure than photos – which anyone online can capture and manipulate – templates, too, can be stolen. Once that happens, these digital keys create a lifelong vulnerability. If a facial recognition database is breached, the “locks” that a template opens – accessing a bank app, getting through security at an airport, entering an office building – can’t be reset. A person’s face is permanent, and so is the threat.
The threat isn’t theoretical. Biometric data has been stolen in data breaches. In 2024, biometric data from a facial recognition system used at bars and clubs in Australia was hacked. And in 2019, biometric data from a pilot facial recognition system set up by U.S. Customs and Border Protection was breached in an attack on a subcontractor’s network. It’s not clear whether anyone’s stolen biometric data has been exploited, however.

AP Photo/Matt Slocum
Tracking your face
All biometric identifiers carry risks. Fingerprints and iris scans, however, are typically used in controlled situations, such as unlocking a person’s phone or allowing someone to enter a building. In these cases, a person has to deliberately look at a scanner. Cameras in public spaces, in contrast, can capture faces as people walk by, from a distance and without the people whose faces are scanned realizing it.
If a fingerprint or iris database is breached, a thief still needs to physically present that finger or eye, or a fake of it, to a scanner. However, someone could match a stolen facial template against images from surveillance cameras or photos circulating online, making it easier to identify a person of interest or track someone’s movements and activities.
There’s also a big difference, technically and ethically, between keeping a face on a phone versus handing it over to a database. On modern Apple devices and many Android systems, biometric data used to unlock the devices is stored locally in a dedicated hardware chip and is not shared with the manufacturer or cloud services for authentication. As a result, a breach of corporate or cloud systems would not expose these device-level biometric templates.
Some street and security cameras in public are passive, just watching as people pass by, with no long-term records. But others may be following people’s steps, linking faces to databases and creating a persistent digital trail. The risk rises when organizations use systems to track particular people across multiple databases. Airport systems could compare a traveler’s face against passport or airline databases. Stadiums may compare faces against local security watch lists or law enforcement lists. The company that manages Madison Square Garden has used facial recognition to bar entry to lawyers at firms that represented people who sued the company.
Some large retail chains, such as Wegmans and Target, also use facial recognition systems in their theft prevention efforts. Every new capture adds another permanent record.
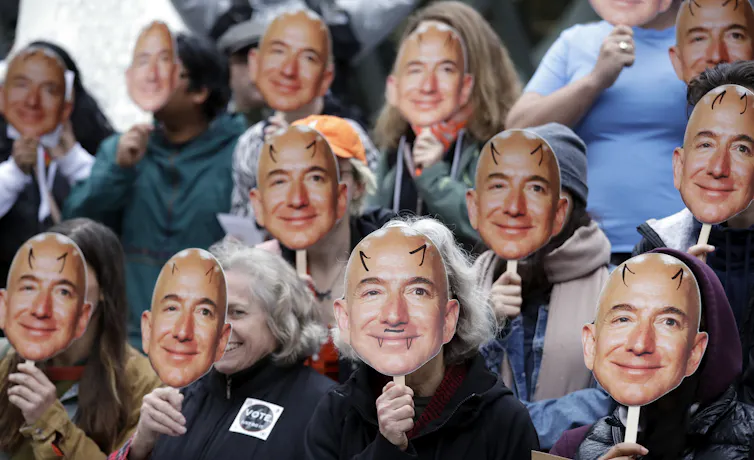
AP Photo/Elaine Thompson
Many companies do not have expertise in cybersecurity and rely on third-party vendors to manage their data. If those centralized systems are breached – or the datasets are linked across platforms, vendors or data brokers – your face can become a sort of persistent identifier, which can be used to expose or track you. In some cases, when combined with other compromised data, your captured face can lower the barrier to impersonating you.
When a person’s face meets their data
A face can function like a “primary key” – a unique and stable identifier that connects records. If one database links a facial template to an email address, and a data breach connects that email to financial or personal records, an identity thief with a stolen template could access all that information.
And combining a template with AI tools such as deepfakes or three-dimensional face models could, in some cases, allow a criminal to impersonate an individual in systems that require proof of a live face, slipping into a forged digital identity like slipping into a costume.
When criminals combine biometric templates with other leaked data, such as logins for social media profiles or home addresses, they can build “super-profiles” connected to many of a person’s activities. Because the face acts as a permanent linking key, this level of identity theft is difficult to reverse.
How to minimize the threat
People are still figuring out how to live with widespread biometric collection. The convenience of smoothly passing security checks or making purchases is appealing, but it often comes with a permanent risk to privacy and security.
To lessen the threat, organizations can follow several data privacy best practices. They can keep only information that is necessary, erase the rest quickly and encrypt every mathematical template. They can store only encrypted templates rather than raw photos. They can use safeguarding techniques, such as the latest liveness detection techniques, to help ensure that their systems are interacting with real people rather than photographs, masks or deepfakes. And they can adopt a privacy-by-design approach, which means they will keep data only as long as necessary, clearly document how it’s used and restrict who has access.
Consumers can take steps as well. In places with privacy laws, such as California, Illinois and the European Union, people can submit a data access request to see what biometric data a company holds and, in some cases, ask for its deletion. They can also ask retailers anywhere what data is collected, how long it is kept and how it’s protected.






